Software & Tools
On this page you can find the software, tools and demonstrators that are developed in the context of CROSSING.
A central goal of CROSSING is to collaboratively develop CogniCrypt, an intelligent open-source platform for hosting cryptographic components (developed in the CROSSING projects or outside of CROSSING) that actively assists application developers in selecting and correctly integrating its components into applications.
Further details can be found on the CogniCrypt webpage.
CogniCrypt is an official Eclipse project since December 2017.
https://www.eclipse.org/cognicrypt/
Authors: Daniel Demmler, Thomas Schneider, Michael Zohner (CROSSING Project E4)
Published: In 21st Network and Distributed System Security Symposium (NDSS'15)
http://encrypto.de/papers/DSZ15.pdf (PDF file) (opens in new tab)
Description: ABY is a framework for implementing secure two-party computation protocols in three different domains that allows to freely and efficiently convert between them. ABY enables the developer to abstract from smaller protocol building blocks in order to realize complex applications.
Target group: Developers
Software development phase: Implementation
Application environment: Secure Computation Protocols
Programming language: C/C++
Software Repository: https://github.com/encryptogroup/ABY
Authors: Dominik Bollmann, Steffen Lortz, Heiko Mantel, Artem Starostin (CROSSING Project E3)
Published: 11th International Conference on Information Systems Security (ICISS'15)
Description: The Assistant for Developing Leak-free Programs (Adele) is an Eclipse-Plugin for the static detection of information leaks in Java source code. It supports programmers in the development of secure software by providing them feedback about possible security issues in their source code as they write it. Adele provides an overview of possible security violations and highlights them in the program's source code. Further information can be found here.
Target group: Software Developer, Programmer
Software development phase: Implementation, Testing
Application environment: Usable as Eclipse-Plugin and Command-Line Tool
Programming language: Java
License: MIT License (http://opensource.org/licenses/MIT)
Authors: Johannes Späth, Lisa Nguyen Quang Do, Karim Ali, Eric Bodden (CROSSING Project E1)
Description: Boomerang is a demand-driven, flow-, field-, and context-sensitive pointer analysis for Java programs. Boomerang computes rich results that include both the possible allocation sites of a given pointer (points-to information) and all pointers that can point to those allocation sites (alias information). For increased precision and scalability, clients can query Boomerang with respect to particular calling contexts of interest.
Download: https://github.com/uasys/boomerang
Authors: Dr. Lucas Davi (CROSSING Project S2), Prof. N. Asokan (University of Helsinki)
Published: In ACM CCS '16
Description: Control- FLow ATtestation (C-FLAT) enables remote attestation of an application's control-flow path.
Download: https://github.com/control-flow-attestation/c-flat
Target group: Security Practitioners, Embedded System Developers
Software development phase: Implementation, Testing
Application environment: Stand-alone C / ARM Assembler implementation
Programming language: C, ARM Assembler
Authors: CROSSING Project E3 (with Boris Köpf for 0.2b)
Description: CacheAudit 0.2b and CacheAudit 0.2c are extensions of the tool CacheAudit [Doychev,Köpf,Mauborgne,Reinecke2015] to cope with standard AES implementations (e.g., OpenSSL, mbedTLS) and to support analysis of the lattice-based security scheme ring-TESLA. They take as input an x86 binary and return upper bounds on the side-channel leakage of the binary with respect to four attacker models.
Download: http://www.mais.informatik.tu-darmstadt.de/cacheaudit-essos17.html
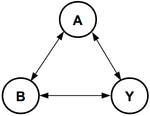
A Robust Bayesian Trust Model for Humans and Agents
In the vision of ubiquitous computing, the activities of daily life are supported by a multitude of heterogeneous, loosely coupled computing devices. The support of seamless collaboration between users, as well as between their devices, can be seen as one of the key challenges for this vision to come true.
This project provides a trust based approach to supporting the selection of trustworthy interaction partners. The goal of this approach is to estimate an entity's trustworthiness as accurately as possible in order to improve the average quality of the entity's interactions. An online demonstrator is also available. More information can be found here.
Download: CertainTrust SDK 1.0
Authors: Lisa Nguyen Quang Do, Karim Ali, Benjamin Livshits, Eric Bodden, Justin Smith, Emerson Murphy-Hill (CROSSING Project E1)
Description: The Just-in-Time analysis concepts aims at making static analysis more usable to the end user, often the code developer. It allows analysis writers to encode prioritization properties into the analysis. At runtime, certain paths are analyzed before others, allowing important results to be returned first. CHEETAH is an implementation of the Just-in-Time analysis concept for taint analysis for Android applications. It is integrated in the Eclipse IDE as a plugin.
Download: https://github.com/secure-software-engineering/cheetah
Authors: Andreas Holzer, Martin Franz, Niklas Büscher, Stefan Katzenbeisser, Helmut Veith (CROSSING Project S5)
Description: CBMC-GC is a compiler for C programs in the context of secure two-party computation (STC). It compiles a C program that specifies a secure computation into a circuit which can be read in by an STC platform, which then performs the secure computation between two parties A and B.
Download: http://forsyte.at/software/cbmc-gc/
Authors: Amit Klein, Vladi Kravtsov, Alon Perlmutter, Haya Shulman, Michael Waidner (CROSSING Project S3)
Description: DNS X-ray tool enables evaluation caches for vulnerabilities to records' injection. The tool also performs fingerprinting of software and operating system of the caches.
Download: http://dns.xray.sit.fraunhofer.de/
Authors: Tianxiang Dai, Haya Shulman, Michael Waidner (CROSSING Project S3)
Description: Misconfigurations in Signed Domains
Download: https://dnssec.cad.sit.fraunhofer.de/
Authors: Markus Schmidt (supervised by Nina Bindel) (CROSSING Project P1)
Description: The LWE-Estimator is an online tool to estimate the concrete hardness of LWE. In our extension we added the ability to estimate the hardness with respect to a given number of LWE samples.
Download:bitbucket.org/malb/lwe-estimator from commit-id eb45a74 on

Authors: Gilad Asharov, Yehuda Lindell, Thomas Schneider, and Michael Zohner (CROSSING Project E4)
Published: In 20th ACM Conference on Computer and Communications Security (CCS'13)
Description: This tool implements an OT extension protocol that has less communication and computation complexity than the original OT extension protocol by Ishai et al. (CRYPTO'03) and thereby achieves a runtime improvement of at least factor 3 over existing OT extension implementations. It supports highly parallel architectures by running in a block-wise and multi-threaded fashion. Moreover, it implements the correlated and random OT functionality, which allows several secure computation protocols to further decrease the amount of data that has to be sent over the network. The tool can be applied in a wide range of deployment scenarios by allowing the designer to choose between different levels of security as well as underlying cryptographic assumptions.
This tool can be used for the development of privacy preservingapplications as well as a tool to protect information in applications.
Target group: Developer
Software development phase: Implementation
Application environment: Secure computation protocols
Programming language: C/C++
Software Repository: http://encrypto.de/code/OTExtension

Authors: CROSSING Project E1
Description: FlowDroid is a context-, flow-, field-, object-sensitive and lifecycle-aware static taint analysis tool for Android applications. Unlike many other static-analysis approaches for Android we aim for an analysis with very high recall and precision. To achieve this goal we had to accomplish two main challenges: To increase precision we needed to build an analysis that is context-, flow-, field- and object-sensitive; to increase recall we had to create a complete model of Android’s app lifecycle.
Download: https://github.com/secure-software-engineering/soot-infoflow-android/wiki

Authors: Julien Bringer, Herve Chabanne, Melanie Favre, Alain Patey, Thomas Schneider, Michael Zohner (CROSSING Project E4)
Published: In 2nd ACM Workshop on Information Hiding and Multimedia Security (IHMMSEC'14) Download (PDF file) (opens in new tab)
Description: GSHADE is a tool for privacy-preserving distance computation which can be used for privacy-preserving biometric identification. GSHADE supports the following distance metrics: Hamming distance, normalized Hamming distance, Euclidean distance, and Scalar product.
Target group: Developers
Software development phase: Implementation
Application environment: Secure Computation Protocols
Programming language: C/C++
Software Repository: https://github.com/encryptogroup/GSHADE
Authors: Johannes Späth, Karim Ali, Eric Bodden (CROSSING Project E1)
Description: IDEal is an alias-aware extension to the framework for Interprocedural Distributive Environment (IDE) problems. It allows to customize object-sensitive data-flow analyses and automatically reasons about aliasing on-the-fly.
Download: https://github.com/uasys/ideal
Authors: Hong Linh Thai, Christian Klos (supervised by Nina Bindel) (CROSSING Project P1)
Description: This software is a fork of GnuPG with integration of the lattice-based signature scheme ring-TESLA.
Download: https://github.com/hlThai/gpg-TeslaRing
Authors: Johannes Buchmann, Niklas Büscher, Stefan Katzenbeisser, Juliane Krämer, Daniele Micciancio, Sander Siim, Christine van Vredendaal, Michael Walter, Florian Göpfert (CROSSING Project P1)
Description: The LWE Challenge
Download: https://www.latticechallenge.org/lwe_challenge/challenge.php

Authors: Wilko Henecka, Thomas Schneider (CROSSING Project E4)
Published: In: 8th ACM Symposium on Information, Computer and Communications Security (ASIACCS'13)
Description: The tool is an improved implementation of Yao’s garbled circuit protocol in the semi-honest adversaries setting which is up to 10 times faster than previous implementations. Its improvements include
- the first multi-threaded implementation of the base oblivious transfers resulting in a speedup of a factor of two
- techniques for minimizing the memory footprint during oblivious transfer extensions and processing of circuits
- compilation of sub-circuits into files, and
- caching of circuit descriptions and network packets.
This tool can be used for the development of privacy preserving applications as well as a tool to protect information in applications.
Target group: DeveloperSoftware development phase: ImplementationApplication environment: Compiler for Memory-Efficient Two-Party Secure Function EvaluationProgramming language: JavaSoftware Repository: encrypto.de/code/me-sfe
Authors: Daniel Steinmetzer, Jiska Classen, Matthias Hollick (CROSSING Project S1)
Description: mmTrace is a deterministic image-based ray-tracing simulation framework for mm-wave propagation developed in MATLAB. It supports the design of mm-wave specific protocols and, in contrast to common statistical models, deals with multiple transceivers. The strengths of mmTrace constitute signal variations at different receivers and interference of multiple transmitters, which are crucial in certain situations. It generates channel impulse responses and determines signal characteristics in arbitray scenarios.
Download: https://github.com/seemoo-lab/mmTrace
Title: Private set intersection for unequal set sizes with mobile applications
Authors: Ágnes Kiss, Jian Liu, Thomas Schneider, N. Asokan, Benny Pinkas (CROSSING Project E4)
Published: In Proceedings on Privacy Enhancing Technologies (PoPETs), 2017(4)(Download (PDF file) (opens in new tab))
Description: We transformed four existing PSI protocols into the so-called precomputation form such that in the setup phase the communication is linear only in the size of the larger input set, while in the online phase the communication is linear in the size of the smaller input set. The implementation contains all four protocols and can be used to run experiments between two PCs and between a PC and a smartphone to create a systematic comparison of their performance.
Target Group: Developers
Software Development Phase: Implementation
Application Environment: Secure Computation Protocols
Programming Language: C/C++/Java
Software Repository: http://encrypto.de/code/MobilePSI
Authors: Lennart Braun, Daniel Demmler, Thomas Schneider, and Oleksandr Tkachenko (CROSSING Project E4)
Published: In ePrint Report 2020/1137 Download
Description: A fast, flexible, and asynchronous C++ framework for secure multi-party computation with N parties, full-threshold security, and conversions between all protocols.
Target Group: Developers
Software Development Phase: Implementation
Application Environment: Secure Computation Protocols and Applications
Programming Language: C/C++
Software Repository: https://github.com/encryptogroup/MOTION
Authors: Daniel Demmler, Marco Holz, and Thomas Schneider (CROSSING Project E4)
Published: In 15th International Conference on Applied Cryptography and Network Security (ACNS'17) (Download) (PDF file) (opens in new tab)
Description: We proposed and implemented OnionPIR, an anonymous messaging service as an example application for PIR combined with onion routing that prevents the leakage of communication meta-data. The evaluation of this prototype shows that OnionPIR is usable in practice.
Target Group: Developers
Software Development Phase: Implementation
Application Environment: Secure Computation Protocols
Programming Language: C/C++
Sourcecode Repository: https://github.com/encryptogroup/onionPIR
Authors: CROSSING Project E1
Description: OPAL is an Open, extensible Analysis Library for Java bytecode which is written in Scala and which consist of multiple projects which build on top of each other. At the core is a newly developed, highly configurable and adaptable bytecode toolkit. On top of that we provide you with a framework for the abstract interpretation of Java Bytecode. These two frameworks are the foundation for various tools targeted towards developers who want to improve the quality of their software. In particular tools for specifying and validating software architectures as well as for finding bugs.
OPAL Project: http://www.opal-project.de/
Sourcecode repository: https://bitbucket.org/delors/opal
Contactperson: Michael Burger (CROSSING Project P1)
Download: https://github.com/MiBu84/p3enum
Contact person: Ágnes Kiss (CROSSING E4 – Compiler for Privacy-Preserving )
Description: Private decision tree evaluation based on homomorphic encryption and/or garbling techniques.
Our implementation for private decision tree evaluation protocols includes the protocols HHH, HGH, GGH, GGG and HGG (it can also be used to benchmark the last and most inefficient protocol HHG). The implementation of (SelH+)CompH and PathH is based on the mcl library (https://github.com/herumi/mcl) that implements efficient lifted ElGamal encryption over elliptic curves, more specifically on the XCMP protocol implementation which implements the DGK comparison protocol (https://github.com/fionser/XCMP). The implementation of SelH, SelG, CompG and PathG are based on the ABY framework (https://github.com/encryptogroup/ABY) which provides an efficient implementation of Yao's garbled circuit protocol as well as of the Paillier homomorphic encryption scheme.
This code is provided as a experimental implementation for testing purposes and should not be used in a productive environment. We cannot guarantee security and correctness.
Download: https://github.com/encryptogroup/PDTE

Authors: Benny Pinkas, Thomas Schneider, Michael Zohner (CROSSING Project E4)
Published: In 23rd USENIX Security Symposium (USENIX'14) http://encrypto.de/papers/PSZ14.pdf (PDF file) (opens in new tab)and 24th USENIX Security Symposioum (USENIX'15) http://encrypto.de/papers/PSZ15.pdf (PDF file) (opens in new tab)
Description: Many actions in the digital world require the user to reveal his complete data. However, often the user does not want all of his data to be disclosed to a third party. For example, when using mobile messaging apps, the app requires access to the user's address book in order to identify the contacts that also use this app. This tool implements Private Set Intersection (PSI) protocols, a cryptographic technique, which allows a secure identification of common contacts, without disclosing any other data. The implemented PSI protocols thereby enable a user-controlled and privacy-preserving comparison of data.
Target group: Developers
Software development phase: Implementation
Application environment: Secure Computation Protocols
Programming language: C/C++
Software Repository: http://www.encrypto.de/code/PSI
Contactperson: Nikolaos Athanasios Anagnostopoulos (CROSSING Project P3)
Published:
Description: We have implemented a toolkit for the assessment of PUFs based on well-known metrics and for the generation of cryptographic tokens based on their responses. Implemented metrics include Hamming weight, intra- and inter-device Hamming distance, (Shannon) entropy, min-entropy and intra- and inter-device Jaccard index. Cryptographic tokens can be produced using a Golay- or a BCH-ECC-based fuzzy extractor. Parts of this toolkit have been integrated into CogniCrypt.
Target group: Developers
Software development phase: Implementation
Programming language: C/C++
Software Repository: https://github.com/prankurgit/PUF_Toolkit/
Authors: Niklas Büscher, Stefan Katzenbeisser (CROSSING Project S5)
RAM based secure computation (RAM-SC) combines Secure Multi-party Computation (MPC) with Oblivious RAM (ORAM). Unfortunately, realizing efficient RAM-SC applications by hand is a tedious and error-prone task, which requires expert knowledge in both cryptographic primitives and circuit design. To make things worse, a multitude of ORAMs with different trade-offs has been proposed. To overcome this entry barrier to RAM-SC, we present an ORAM library and an extension to our CBMC-GC compiler that analyzes the input source code and extracts relevant information about the usage patterns of all arrays in the code. The results of the analysis are then used to predict the runtime of suitable ORAMs and to identify the ORAM that achieves minimal runtime. Thus, for the first time, RAM-SC also becomes accessible to non-domain experts.
Web page: https://gitlab.com/securityengineering/ram-sc-for-cbmc-gc
Authors: Yossi Gilad, Amir Herzberg, Michael Schapira, Haya Shulman (CROSSING Project S3)
Description: Automated evaluation of deployment of cryptography for BGP, misconfigurations and vulnerabilities.
Download: http://roalert.org/
Authors: CROSSING Project E3
Description: The Side-Channel FinderAVR is a tool for checking AVR assembly programs for timing-side-channel leakage. It takes as inputs an AVR assembly program and a configuration specifying which information is considered secret. The tool either returns with a success or with a failure report. In case of a success, the AVR assembly program is secure. In case of a failure report, the developer is pointed to a location in the code that potentially introduces timing-side-channel leakage. The Tool is based on a security type-system that is sound with respect to timing-sensitive noninterference.
Download: http://www.mais.informatik.tu-darmstadt.de/scf2017.html
Authors: CROSSING Project E1
Description: Soot is one of the most widely used analysis and transformation frameworks for Java bytecode and source code. Soot features a wide-range of intermediate representations that make static program analysis as easy as it can be. While Soot is not our own development, we are maintaining the framework at the moment. It was developed at the Sable Research Group of McGill University, but with contributions by other researchers from all over the world. Many of our existing tools are based on Soot and/or integrate with it. Further Information can be found here.
Target group: Programmer
Software development phase: Implementation
Application environment: Java, Eclipse Plugin
Programming language: Java License: LGPL 2.1
Authors: Sheikh Mahbub Habib, Max Mühlhäuser (CROSSING Project S1)
Description: TaaS4Cloud, a web service, which is developed for potential cloud users to assess the level of cloud providers’ security capabilities. It considers provider supplied public information from the CSA STAR in order to assess and quantify the security capabilities. The level of security capabilities is communicated to potential cloud service users via numerical score and intuitive graphical interfaces.
Authors: Daniel Steinmetzer, Daniel Wegemer, Matthias Hollick (CROSSING Project S1)
Description: The Talon Tools project consolidates a set of software tools for practical research with commodity IEEE 802.11ad devices. It bases on TP-Link's Talon AD7200, which is the first wireless router that supports the IEEE 802.11ad standard and was released in 2016. Using this platform allows to investigate various aspects of 60 GHz millimeter-wave communication in realistic on-site experiments. With our framework, we support various kinds of experiments and evaluations performed with multiple routers in arbitrary environments.
Authors: Sedat Akleylek, Erdem Alkim, Nina Bindel, Johannes Buchmann, Özgür Dagdelen, Edward Eaton, Gus Gutoski, Juliane Krämer, Giorgia Azzurra Marson, and Filip Pawlega (CROSSING Project P1)
Description: TESLA is a lattice-based signature scheme from the learning with errors problem that is secure even against quantum adversaries. The signature scheme ring-TESLA is the more efficient variant of TESLA over ideal lattices.
Download: https://tesla.informatik.tu-darmstadt.de/de/tesla/
Title: Implementation of Valiant's Universal Circuit Construction Optimized for Private Function Evaluation
Authors: Ágnes Kiss, Thomas Schneider (CROSSING Project E4)
Published: In 35th Advances in Cryptology (EUROCRYPT'16)(Download) (PDF file) (opens in new tab)
Description: Our Universal Circuit Compiler implements the most efficient UC construction, originally proposed by Leslie G. Valiant in STOC`76. It accepts any Boolean circuit as input in SHDL format, provided that the gates have at most two incoming edges, and outputs the topology of the UC along with its programming bits corresponding to the circuit.
Target Group: Developers
Software Development Phase: Implementation
Application Environment: Secure Computation Protocols
Programming Language: C/C++
Sourcecode Repository: https://github.com/encryptogroup/UC
Authors: Lisa Nguyen Quang Do, Stefan Krüger, Patrick Hill, Karim Ali, Eric Bodden (CROSSING Project E1)
Description: VisuFlow is a debugging environment designed to support static analysis writers understand and debug an analysis. It is written as an Eclipse plugin, and supports static data-flow analyses written on top of the Soot analysis framework.
Download: https://github.com/VisuFlow
Authors: Project Quantencomputer-resistente Signaturverfahren für die Praxis / squareUP --- Stefan-Lukas Gazdag (genua GmbH), Denis Butin (CDC)
Published: IRTF Internet-Draft draft-irtf-cfrg-xmss-hash-based-signatures-03 (https://datatracker.ietf.org/doc/draft-irtf-cfrg-xmss-hash-based-signatures/)
Description: The hash-based signature scheme XMSS is specified in the Internet-Draft “XMSS: Extended Hash-Based Signatures”. Hash-based signatures are the first post-quantum signature scheme undergoing standardisation. This open source implementation closely follows the Internet-Draft, and is available on the squareUP project website (http://www.pqsignatures.org/index/publications.html#code).
Target group: Standardisation and specification organisation members, stakeholders
Software development phase: Cross-tested, available
Application environment: Stand-alone C implementation, OpenSSL dependency
Programming language: C
License: BSD License











